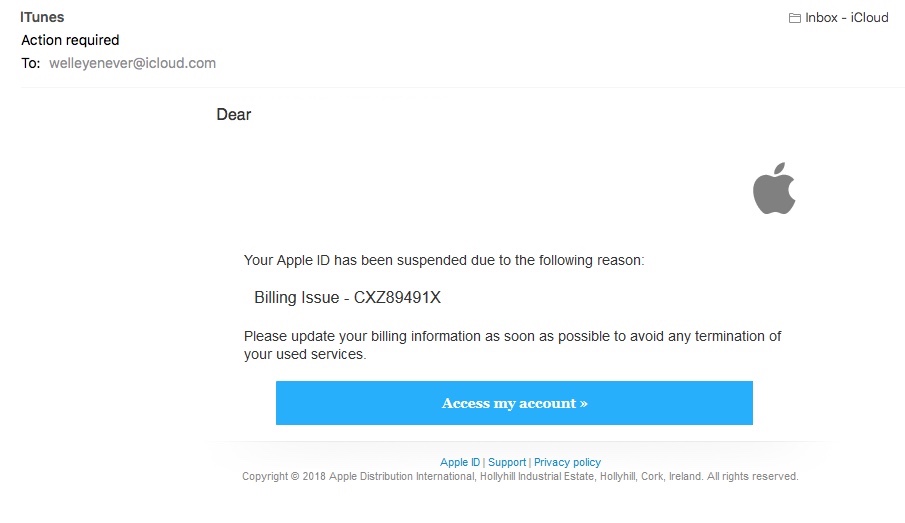
I’ve had another scam email recently that I wanted to quickly share with you, because it’s another one that’s fairly common, similar to ones for Paypal. But this time it’s from someone pretending to be iTunes, which is of course used by millions of people, myself included.
It’s a very short email, and the main red flags are very easy to spot. However, it does have a sneaky trick up its sleeve to be careful of, that I’ve not seen in my other spam emails so far.
Update: Since writing this post, I’ve had a 2nd email, which is identical except for a few minor differences, which I’ve noted below as well.
The Email
Firstly, it’s important to note that Apple never send out messages like this. They’re very security conscious. But regardless of that, this is easy to pick apart anyway.
From Name: iTunes
From Addresses
- Email 1:
Servic732893266249432556284429544262@Servid7883493458543950.com- Email 2:
wsercodmltune837200cknfdv7834rkdn934fkmdv49fvkjn@nvjhcxddkmccostacomd.comSubject:
- Email 1: Action required
- Email 2: Please update your billing information
Message:
[Email Address],
Your Apple ID has been suspended due to the following reason:
Billing Issue – CXZ89491X
Please update your billing information as soon as possible to avoid any termination of your used services.
Access my account [Button points to 5.189.146.107/~calmbunn/.uk/uk/index.php]
From Address
The sender’s name says it’s from iTunes, but the actual address is clearly randomly generated and has nothing to do with Apple:
- Servic732893266249432556284429544262@Servid7883493458543950.com
- wsercodmltune837200cknfdv7834rkdn934fkmdv49fvkjn@nvjhcxddkmccostacomd.com
Message
The salutation greets me by my email address, not my name, which iTunes would have on file. Though as it happens, the address I use for my blog isn’t the one I use for iTunes anyway, so it’s impossible for iTunes to suspend an account that doesn’t exist!
The rest of the message is short and has no spelling errors, so perhaps isn’t quite so obvious. The phrasing “termination of your used services” is rather odd grammatically though, but otherwise there’s not a lot to say about that aspect of it.
Link
Hovering over the link to view the address again shows that it has nothing to do with Apple, as it’s pointing to “5.189.146.107/~calmbunn/.uk/uk/index.php”.
Many scam emails include the company name in the link address somewhere, to try and give the impression it’s genuine, even though it’s still obviously fake. But here the scammer’s just been very lazy and picked a very random address. They haven’t even set up a proper website name, it’s just an IP address, which could potentially be useful for tracing purposes.
But here’s the interesting thing – the button isn’t actually the link. Sure, you can click on it and it will take you to that website. But you can also click anywhere else for the same effect, because the entire message is a clickable image.
So this includes the white background, the Apple logo, the message text, the account access button, and the footer text with what appear to be links for the Apple ID, Support and Privacy Policy along with the Apple copyright line. Clicking any of those things will take you to that dodgy website. The only exception is the initial salutation to my email address, which is standard text, as it’s their only way of trying to make the email appear personalised.
I noticed it was an image when I went to copy and paste the text for this post. I saw my mouse cursor was a pointing hand icon wherever I moved it in the message, rather than a regular arrow. It only changes to the hand icon when it’s over a link. And resting the cursor over parts of the message away from the button continued to reveal the address as a tooltip. So there was no text to copy – I simply typed up a copy by hand instead.
There is a bit of clear space either side of the image, because they’ve centred it in the message window, so if your window is wide enough, you can potentially click to the left and right of the image safely. But overall it’s easy for you to hit the link anywhere without expecting to, e.g. if you were to try and click the Support link at the bottom or just randomly clicked anywhere on the message in general. So that is a sneaky little trick.
Looking at the source code, we find that the actual image is stored on a legitimate picture hosting site called imgBB:
- Email 1: https://image.ibb.co/k1Sjqp/2036.png
- Email 2: https://image.ibb.co/eEb7Sp/2037.png
Apart from giving you a bigger target to click on, the scammer has also used an image rather than text in this instance, to try and bypass spam checks by email providers. It’s difficult to analyse the text of an email for spam if there’s no text to begin with. It is possible to detect text in images using OCR (Optical Character Recognition), but I don’t know if email companies do that.
Also, can I just point out that the image doesn’t have Alt Text to describe it either. Screen reading software, which speaks the content of web pages to visually impaired people, will look for and read out the Alt Text attributes where available. So it’s important to use it to describe your images. Otherwise, the screen reader will just say it’s an image and nothing more, which is meaningless, and that’s the case here. Which isn’t a surprise. Scammers don’t care about anybody, so of course they’re going to be discriminatory and ableist too, right? I mention Alt Text more in this post incidentally – if you’re not adding image descriptions on your blog, Twitter, etc, please do, it’s important.
Footer
Weirdly, there’s a big space below the clickable image. And if you scroll all the way down to the bottom, there’s this:
Unsubscribe
gboticia 1 Hillcrest Road <a href=”https://www.w3schools.com/html/”>Visit our HTML tutorial</a> Tiburon, US-CA 94920 United States (625) 985-2234
The unsubscribe links points to an Infusionsoft unsubscribe address:
https://eb512.infusionsoft.com/app/optOut/0/7a6a0678b5aa2e8f/29411/93ae9e55efb87b26
That appears to be genuine, because after the https:// prefix the first forward slash comes after “infusionsoft.com”, which is their correct website name.
The w3schools link is also genuine – that’s actually quite a useful website for learning the basics of HTML code – although what doesn’t make sense is why it’s in the middle of the company postal address.
The source code also reveals they’ve left in a tracking pixel, which is an unseen image just 1 pixel in size, that mail senders use to detect if you’ve opened their message or not. That appears to be related to the Infusionsoft message as well, I don’t think it’s being used by the scammer.
All this basically means is that the scammer has copied an email from Infusionsoft that was originally genuine, stripping out Infusionsoft’s content and replacing it with their own. But they’ve either done a terrible job and left a mess behind, or they’ve deliberately left in HTML code and tracking pixel from a real email in order to try and fool spam filters that the message is genuine. Both options are very possible.
Either way though, the From address and the website link, along with the fact that Apple never send out emails like this in the first place, are enough to show that it’s obviously fake. The warning signs are still very prominent. So stay vigilant as always!


2 thoughts on “Scam Email – Apple iTunes”