Back in April I did a post about scam emails I’d had pretending to be from Amazon and Barclays (and a shoutout to Codemefy who commented on it – go and check out their blog for lots of spam email information).
It’s always been my intention to make more scam awareness posts like that, to keep raising awareness, but time’s not been on my side. However, I will keep them coming here and there, and today I wanted to share an email I got at work this week, from a scammer pretending to be Microsoft. Given that it was at my workplace, it suggests this is more aimed at business people rather than home users, but you never know who will receive these things. It is the sort of email that people at home could fall for too if they’re not careful.
The Email
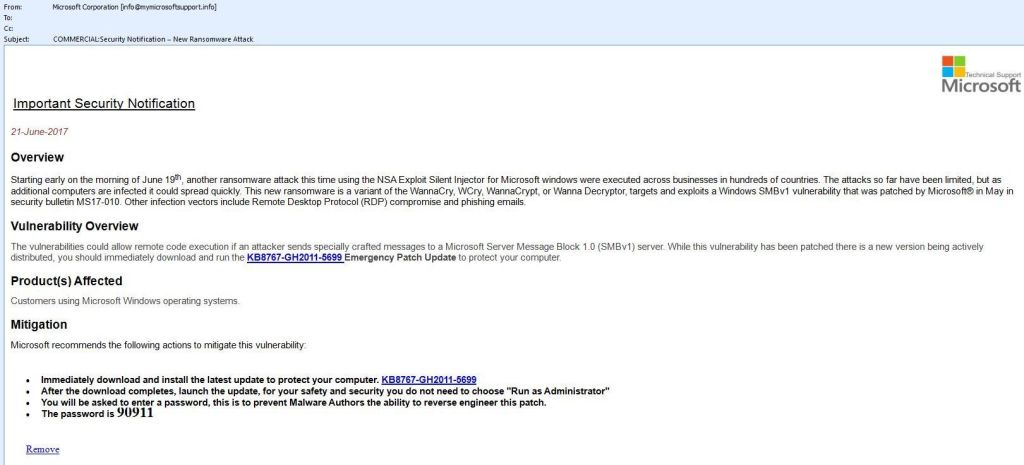
From: Microsoft Corporation (info @ mymicrosoftsupport . info)
Subject: Security Notification – New Ransomware Attack
Important Security Notification
21-June-2017
Overview
Starting early on the morning of June 19th, another ransomware attack this time using the NSA Exploit Silent Injector for Microsoft windows were executed across businesses in hundreds of countries. The attacks so far have been limited, but as additional computers are infected it could spread quickly. This new ransomware is a variant of the WannaCry, WCry, WannaCrypt, or Wanna Decryptor, targets and exploits a Windows SMBv1 vulnerability that was patched by Microsoft® in May in security bulletin MS17-010. Other infection vectors include Remote Desktop Protocol (RDP) compromise and phishing emails.
Vulnerability Overview
The vulnerabilities could allow remote code execution if an attacker sends specially crafted messages to a Microsoft Server Message Block 1.0 (SMBv1) server. While this vulnerability has been patched there is a new version being actively distributed, you should immediately download and run the KB8767-GH2011-5699 Emergency Patch Update to protect your computer.
Product(s) Affected
Customers using Microsoft Windows operating systems.
Mitigation
Microsoft recommends the following actions to mitigate this vulnerability:
- Immediately download and install the latest update to protect your computer. KB8767-GH2011-5699
- After the download completes, launch the update, for your safety and security you do not need to choose “Run as Administrator”
- You will be asked to enter a password, this is to prevent Malware Authors the ability to reverse engineer this patch.
- The password is 90911
Remove
The Background
To put this in context, this is an attempt to cash in on people’s fears and security concerns after the recent WannaCry ransomware attack which dominated the headlines. Here in the UK it severely disrupted computer systems used by the National Health Service (NHS), and it affected many other systems around the world too.
It basically encrypted all the files on the system, making them impossible to use, and then tried to get victims to pay a ransom to get things put back to normal. This is a very common method of infecting machines these days, and it’s effective because there are always people who will pay the ransom. They shouldn’t pay, because it’s funding criminal activity and there’s absolutely no guarantee that the ransomware creator will restore the files. But some people do make the payment, because they feel they have no choice.
The advice, as always, is to make sure you have backups! Your most precious data that you cannot afford to lose should be stored on a backup drive that isn’t directly accessible from your machine – because some ransomware may try to infect anything that it can get to via a direct connection or over a network, whether it be over a cable or wireless.
So that’s what this scam is about. And the worrying thing is that, at first glance, it looks like a serious and professional email. There are plenty of signs that it’s rubbish that I’m about to get to, but for people who aren’t so clued up on these things, and who may be worried given all the talk of ransomware, hacking and security concerns in the news, there is fair potential to fall for this.
The Clues
The email does look professional, with a Microsoft logo, structured text, and professional writing for the most part. But as with most spam emails, there are various clues that give away its false nature. In particular, the download link points to an anonymous file sharing site – not Microsoft’s own server – and there are some notable wording and grammatical errors throughout. But even before we get to those, there’s a very simple fact that should make you suspicious from the outset.
Microsoft don’t send messages like this
The first thing is the fact that the message exists in the first place, because Microsoft never sends out emails like this, at least not to my knowledge. If they want to do an update to your Windows PC or network, they can do it through the built-in Windows Update service. That’s what it’s there for.
And even if they do need experienced IT professionals to install things in a different way – e.g. if there’s a fault with Windows Update – then they would issue bulletins on their own site, and make the media aware if absolutely necessary to spread the word. Sending emails out to random people in random companies and random households is certainly not what they do.
So the fact that you’ve got an email from Microsoft should ring alarm bells in itself. It’s the same as when you get a phonecall from someone claiming to be Microsoft, saying there’s something wrong with your PC. Nope, Microsoft never do that either. That’s one of the oldest computer scams around, but a few people must still fall for it to make it worthwhile for the scammers to keep it up. So if you ever get a call supposedly from Microsoft, just hang up. If you ever get an email from Microsoft like this, delete it.
So we already know the message is a con, but let’s go through it bit by bit anyway. The closer you look at these emails, the more they fall apart.
From Address
info @ mymicrosoftsupport . info
I’ve spaced the address out so it doesn’t become an active link. But mymicrosoftsupport.info is not a proper Microsoft site (that would be www.microsoft.com). The spammers could have potentially spoofed the From address to make it look like it came from Microsoft.com, but they didn’t here, content with the fact that having the word ‘Microsoft’ somewhere in the domain will be enough to trick people.
It’s enough to confirm by putting the entire email address, or just the domain part (mymicrosoftsupport.info) into Google’s search box. Doing that brings up a site that lists it as malicious, along with some other links that indicate the site is based in China. So it’s perfectly possible that’s where the scammers are.
Formatting
The formatting of the text is a bit inconsistent here, particularly the colouring. Some text is black, but other passages are more grey. Why, I have absolutely no idea, but it does look odd. There’s no reason why it can’t all be standard black text.
Beyond that, though, it is quite well formatted, with a Microsoft logo, headings, paragraphs and bullet points. So it does look somewhat professional. The Subject line also makes it look important – calling it an Important Security Notification is of course bound to get people’s attention.
Overview Paragraph
This looks professionally written at first glance, but is easy to pick apart. The text doesn’t seem to have been stolen from anywhere (having Googled sections of it to check) – which suggests it’s been written by the scammer. And they haven’t done the great job they think they have.
The first sentence alone has a few issues.
Starting early on the morning of June 19th, another ransomware attack this time using the NSA Exploit Silent Injector for Microsoft windows were executed across businesses in hundreds of countries.
First, although it has one comma, it really needs a couple more to give it a couple of natural pauses (if you imagine speaking it). So let’s add those after “ransomware attack” and “Microsoft windows”:
Starting early on the morning of June 19th, another ransomware attack, this time using the NSA Exploit Silent Injector for Microsoft windows, were executed across businesses in hundreds of countries.
This effectively isolates the central, descriptive part of the sentence. If we take that out, a massive grammatical issue becomes immediately obvious.
Starting early on the morning of June 19th, another ransomware attack were executed across businesses in hundreds of countries.
As you can see in the wording I’ve highlighted, “were executed” implies multiple attacks, but the part before it suggests only one attack took place. It’s totally inconsistent. Either “more attacks were executed” or “another attack was executed”, but not this. Also, shouldn’t it be “early in the morning”, rather than “on”?
And as for the descriptive part we just separated:
this time using the NSA Exploit Silent Injector for Microsoft windows,
Firstly, if you Google “NSA Exploit Silent Injector” – making sure you use the quote marks to search the whole phrase – then you get no results. It does suggest some hacking forums instead, but no sites actually have the phrase “NSA Exploit Silent Injector”. Strange, no?
Also, the word “windows” should have a capital W as it’s the name of the product. The person trying to impersonate a brand is being very sloppy by overlooking that. It is correctly done later on, but the lack of consistency shows a lack of proofreading.
The rest of the Overview paragraph isn’t quite as bad, but still not perfect:
The attacks so far have been limited, but as additional computers are infected it could spread quickly. This new ransomware is a variant of the WannaCry, WCry, WannaCrypt, or Wanna Decryptor, targets and exploits a Windows SMBv1 vulnerability that was patched by Microsoft® in May in security bulletin MS17-010. Other infection vectors include Remote Desktop Protocol (RDP) compromise and phishing emails.
To try and make it look genuine, a lot of terms in this text are real, including the names of the ransomware viruses, and the terms “Windows SMBv1”, “Remote Desktop Protocol” and “infection vector”.
In addition, if you search for the security bulletin, you will indeed find MS17-010 on Microsoft’s official site. It is a genuine, critical notice from Microsoft, and it is related to the Wannacry attacks. But then, if it’s that important, why didn’t they give you a link to the bulletin page? It’s easy enough to do – I just did it, and a professional company like Microsoft would do so.
So the scammer is trying to use that paragraph to persuade that the email is real. It’s not, as we’re already establishing, but it’s a seriously thought-out attempt to con people.
Vulnerability Overview Paragraph
The vulnerabilities could allow remote code execution if an attacker sends specially crafted messages to a Microsoft Server Message Block 1.0 (SMBv1) server. While this vulnerability has been patched there is a new version being actively distributed, you should immediately download and run the KB8767-GH2011-5699 Emergency Patch Update to protect your computer.
The first sentence of this paragraph is lifted almost verbatim from the MS17-010 bulletin page, another attempt to look legitimate. The second sentence again has issues with commas not being placed correctly – and also subtly tries to explain the fact that they’re not using Windows Update to distribute the patch. They’re claiming that it’s already been patched once, but there’s a new version being distributed. But, if that’s the case, why not just distribute it through Windows Update again? That makes no sense.
So what is this update? They are telling people to download the KB8767-GH2011-5699 Emergency Patch Update – and yet, if you Google “KB8767-GH2011-5699”, nothing comes up. Well, nothing other than some page about URL scanners that I didn’t dare click on. Nothing Microsoft-related appears whatsoever in the search results. And when I go to the Microsoft Update Catalog page, searching for the number there brings no results either. In fact, most KB (Knowledge Base) reference numbers I’ve seen look nothing like this – they’re more like KB1234567. That is to say, they have 7 digits after the KB prefix, without any additional letters or dashes.
Furthermore, if you hover over the link in the email to see where it goes, you get a very odd looking address:
rbfi.io/dl.php?key=/9B5s/KB8767-GH2011-5699.exe
That clearly has nothing to do with Microsoft. Instead, Googling rbfi.io shows it to be a site called Robust Files, with the tagline “Anonymous file sharing made simple”.
So rather than using their own servers like they do for all other updates, we’re supposed to believe that Microsoft are using an anonymous file sharing site to send out a critical security fix?
Or is it simply that the person sending the email is a cowardly scammer, hiding behind anonymity to distribute their silly little program? I know what I’m going for!
Mitigation Section
Microsoft recommends the following actions to mitigate this vulnerability:
- Immediately download and install the latest update to protect your computer. KB8767-GH2011-5699
- After the download completes, launch the update, for your safety and security you do not need to choose “Run as Administrator”
- You will be asked to enter a password, this is to prevent Malware Authors the ability to reverse engineer this patch.
- The password is 90911
Remove
Again, the same dodgy link is provided here. And you’re given a password too – in slightly larger print to the rest of the text to make it stand out as well. But Microsoft never issue passwords with updates. Why would they? They built their own operating system, so they don’t need to give you a password to install their own stuff!
In addition, the previous line to the password says that it’s to prevent Malware Authors from reverse engineering the patch. Firstly, “Malware Authors” doesn’t need to be capitalised, unless that’s the name of a company of hackers). But also, they’ll have the password if they read this email anyway, rendering the whole sentence redundant.
It’s also interesting that you don’t need to run the program as administrator either. It’s either happy to do plenty of damage without getting admin access, or it’s designed to use a backdoor into the system if it hasn’t already been patched. And if we’re being picky about grammar, the bit that says “For your safety…” is a new sentence, so there should be a full stop before it, not a comma. Likewise, “this is to prevent…” feels like it ought to be a new sentence as well.
And finally, there’s a link called “Remove” at the very end. When you hover over this, the address it gives is just mailto:?subject=Unsubscribe. This will simply open up a new email message on your system, with the subject line “Unsubscribe” – but with no address to send it to. So it’s a useless link, and I’m not really sure why it’s there. And surely the word “Unsubscribe” would be better if you’re going to do something like that, as “Remove” doesn’t make it clear what you’re removing or from where. The word “unsubscribe” is much more commonly used (albeit often in really, really, really small print at the bottom of many emails in the hope you won’t see it).
And that’s it, I’ve picked that email apart more than enough. Basically, you should always be extremely wary of anybody claiming to be Microsoft offering to ‘fix’ your computer, as it’ll always be a con. Microsoft don’t contact people like that. And you can always contact Microsoft Support yourself (e.g. on Twitter) if you want to double-check.
And never trust phonecalls claiming to be from Microsoft either. It’s fun to watch some people mess with those callers though, there’s loads of examples on Youtube. So I’ll leave you with one of those. Enjoy, and thanks for reading!

